An Inside Look at Defending the Black Hat Network – TY
[et_pb_section fb_built=”1″ admin_label=”section” _builder_version=”4.16″ da_disable_devices=”off|off|off” global_colors_info=”{}” da_is_popup=”off” da_exit_intent=”off” da_has_close=”on” da_alt_close=”off” da_dark_close=”off” da_not_modal=”on” da_is_singular=”off” da_with_loader=”off” da_has_shadow=”on”][et_pb_row admin_label=”row” _builder_version=”4.16″ background_size=”initial” background_position=”top_left” background_repeat=”repeat” global_colors_info=”{}”][et_pb_column type=”4_4″ _builder_version=”4.16″ custom_padding=”|||” global_colors_info=”{}” custom_padding__hover=”|||”][et_pb_code _builder_version=”4.17.6″ _module_preset=”default” global_colors_info=”{}”] [/et_pb_code][/et_pb_column][/et_pb_row][/et_pb_section]
Cybersecurity in the Merger & Acquisition Process – TY
[et_pb_section fb_built=”1″ _builder_version=”4.16″ da_disable_devices=”off|off|off” global_colors_info=”{}” da_is_popup=”off” da_exit_intent=”off” da_has_close=”on” da_alt_close=”off” da_dark_close=”off” da_not_modal=”on” da_is_singular=”off” da_with_loader=”off” da_has_shadow=”on”][et_pb_row _builder_version=”4.16″ background_size=”initial” background_position=”top_left” background_repeat=”repeat” global_colors_info=”{}”][et_pb_column type=”4_4″ _builder_version=”4.16″ custom_padding=”|||” global_colors_info=”{}” custom_padding__hover=”|||”][et_pb_text _builder_version=”4.17.4″ _module_preset=”default” global_colors_info=”{}”] Enjoy the On Demand Webinar [/et_pb_text][et_pb_text _builder_version=”4.17.4″ background_size=”initial” background_position=”top_left” background_repeat=”repeat” global_colors_info=”{}”] [/et_pb_text][et_pb_cta title=”Want to see how we can help keep you safe during a merger or acquisition? Schedule […]
Reveal Your Attack Surface Through Machine Learning Without an Agent, Scans, or Another Data Lake

Stop relying on scans, agents, or other legacy methods for assessing your attack surface and performing vulnerability management. Instead, turn to Machine Learning.
Why Worry About Asset Lifecycle Management?
[et_pb_section fb_built=”1″ admin_label=”section” _builder_version=”4.16″ da_disable_devices=”off|off|off” global_colors_info=”{}” da_is_popup=”off” da_exit_intent=”off” da_has_close=”on” da_alt_close=”off” da_dark_close=”off” da_not_modal=”on” da_is_singular=”off” da_with_loader=”off” da_has_shadow=”on”][et_pb_row admin_label=”row” _builder_version=”4.16″ background_size=”initial” background_position=”top_left” background_repeat=”repeat” global_colors_info=”{}”][et_pb_column type=”4_4″ _builder_version=”4.16″ custom_padding=”|||” global_colors_info=”{}” custom_padding__hover=”|||”][et_pb_text admin_label=”You don’t have to if you don’t want to” _builder_version=”4.16″ _module_preset=”default” global_colors_info=”{}”] You don’t have to if you don’t want to. However, if you ignore it, you might just […]
Master Cybersecurity Through Asset Lifecycle Management
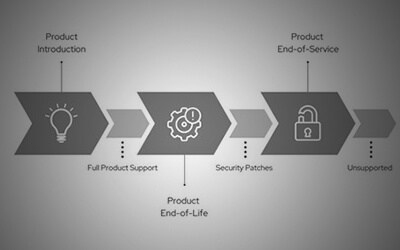
[et_pb_section fb_built=”1″ admin_label=”section” _builder_version=”4.16″ da_disable_devices=”off|off|off” global_colors_info=”{}” da_is_popup=”off” da_exit_intent=”off” da_has_close=”on” da_alt_close=”off” da_dark_close=”off” da_not_modal=”on” da_is_singular=”off” da_with_loader=”off” da_has_shadow=”on”][et_pb_row admin_label=”row” _builder_version=”4.16″ background_size=”initial” background_position=”top_left” background_repeat=”repeat” global_colors_info=”{}”][et_pb_column type=”4_4″ _builder_version=”4.16″ custom_padding=”|||” global_colors_info=”{}” custom_padding__hover=”|||”][et_pb_text admin_label=”With Cloud, Infrastructure as Code, Containers” _builder_version=”4.16″ _module_preset=”default” global_colors_info=”{}”] With Cloud, Infrastructure as Code, Containers, and BYOD to name a few of the rapidly adopting technologies, the struggles with […]
